Hostile acts don’t always arrive with a clear signature.
Nefarious actors shape elections without leaving irrefutable evidence of ballot manipulation. Rogue states interfere with infrastructure through actions that resist clean attribution. State-backed hackers can warp information environments while avoiding immediate blame.
Ambiguity does much of the work, deniability reinforces it, and legal contestability slows responses further. Accumulated over time, such incidents impose economic cost and political strain on targeted nations. They can also create paralysis in terms of how a targeted nation should respond. Governments find it harder to respond when responsibility cannot be firmly established and when the incident falls below the threshold associated with armed retaliation.
Such actions thus sit in the space between routine peacetime activity and open warfare, an area that has come to be known as the “gray zone.”
Where is the ‘gray zone’?
Policy and military communities began using the term “gray zone” in the early 2010s to describe environments in which states pursue an advantage against a rival without crossing a line that would justify the use of overt force in response.
This kind of activity can be sustained and strategically meaningful even when it doesn’t resemble conventional conflict. Russia’s interference in the 2016 U.S. presidential election offers a widely cited case. U.S. intelligence assessments concluded that hacked material was paired with timed disclosure and online amplification, with the aim of eroding confidence in the democratic process.
Cyber operations provide another illustration. The 2015 and 2016 attacks on Ukraine’s power grid – attributed to Russian-linked actors – temporarily disrupted electricity distribution for large civilian populations.
The operations demonstrated Russia’s ability to penetrate critical infrastructure, but stopped short of permanent destruction.
In recent years, maritime infrastructure has entered the same arena. Investigations into damage affecting undersea cables and pipelines in the Baltic Sea following the Nord Stream explosions of Sept. 26, 2022, underscored how difficult attribution can be.
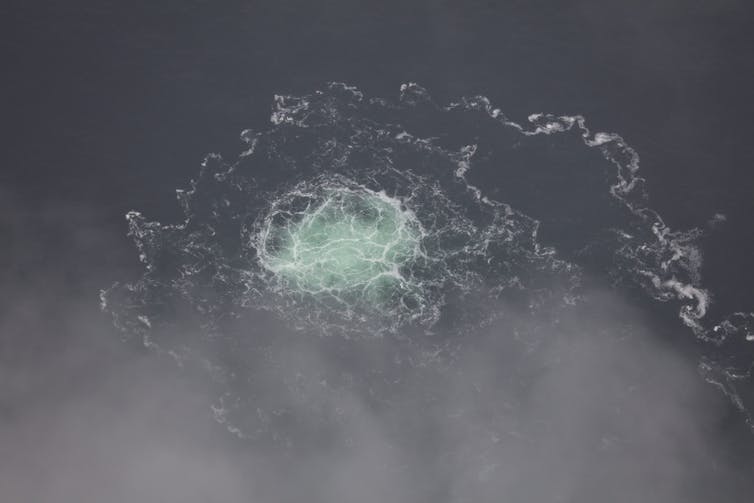
The defining feature of gray zone action lies in its relationship to escalation rather than magnitude. Attacks don’t have to cause immediate, large-scale damage. Rather, each measure is calibrated for deniability and applied episodically.
Meanwhile, legal ambiguity slows retaliation, allowing pressure to build as thresholds are approached, often through areas not traditionally treated as military domains.
Who operates in the gray zone?
Russia has become particularly associated with gray zone tactics. Its campaign against Ukraine did not begin in 2022 but unfolded gradually over years with disinformation campaigns and with cyber intrusions probing institutional resilience. This then developed into Russia using proxy forces in eastern Ukrainian regions and then unmarked Russian personnel appearing during the seizure of Crimea in 2014.
Each move complicated Ukraine’s response, and over time the cumulative effect reshaped the strategic environment before open warfare actually began in February 2022.
China has employed similar methods, especially at sea. In the South China Sea, fishing vessels that are part of China’s maritime militia operate alongside the country’s coast guard to shadow foreign ships, block access to disputed reefs and pressure rival claimants such as the Philippines and Vietnam. These confrontations rarely escalate into naval battles, yet over time they alter control and presence in contested waters without a formal outbreak of war.
Iran’s regional posture reflects another pattern in gray zone tactics. Cyber activity has targeted the infrastructure of Gulf rivals. Meanwhile, commercial shipping has faced harassment through Iran’s proxy actors. Drone and missile strikes by Iran-aligned militias apply added calibrated pressure while insulating Tehran from direct responsibility.
The United States and its allies also operate within this competitive space, relying on tools that remain below the threshold of declared conflict. American cyber units have reportedly penetrated segments of Iran’s military command systems, and covert U.S. assistance to partner forces in places such as eastern Syria has also unfolded without crossing into open interstate war.
Countering gray zone attacks?
Each year brings thousands of state-linked gray zone incidents. Indeed, within NATO and the European Union, this kind of hybrid pressure is now treated less as an anomaly and more as part of the normal landscape of strategic rivalry.
Responses exist, but none of them resolve the problem cleanly.
After the Ukraine grid attacks of the mid 2010s, several European states accelerated cybersecurity investment, improving network segmentation, expanding backup capacity and deepening information sharing with private infrastructure operators.
Collective attribution offers another tool. NATO and the European Union have developed mechanisms for joint public attribution, which increases the probability of diplomatic and economic measures being imposed, even when military response remains inappropriate.
Sanctions imposed on front companies and individual operatives involved in gray zone attacks can manage exposure, but they can’t eliminate vulnerability.
That’s because gray zone competition takes shape inside the systems that sustain modern economic life. Advanced economies depend on infrastructure designed not for defense but efficiency – transnational data networks, integrated energy markets, real-time financial platforms.
These systems move information and capital at extraordinary speed. But they also create openings for interference that can be calibrated to remain below the threshold of armed attack.
Mitigating that exposure is possible, but it comes with economic trade-offs.
That tension helps explain the persistence of gray zone tactics. When direct conflict carries unacceptable escalation risk, sustained pressure below the threshold of force offers states a way to bend the will of a rival nation without triggering open war.
This article is part of a series explaining foreign policy terms commonly used but rarely explained.
Andrew Latham does not work for, consult, own shares in or receive funding from any company or organization that would benefit from this article, and has disclosed no relevant affiliations beyond their academic appointment.
This article was originally published on The Conversation. Read the original article.