Over the past year, SafeBreach researcher and former Brazilian jiu-jitsu athlete Anon Leviev has developed a proof-of-concept Windows Downdate tool. This tool has been demonstrated to invisibly hijack the Windows Update process to make an "invisible, persistent, and irreversible" downgrade to critical OS components. It effectively undoes past security updates and allows an entire system to hijack through any resultant vulnerabilities.
So, good news first: Anon Leviev has only done this to help address these issues and hopefully prevent users and organizations from falling prey to such a malicious cyber attack. Responsible disclosure has been practiced, so Microsoft has been aware of these issues since February 2024, and two official vulnerability pages (CVE-2024-38202 and CVE-2024-21302), which went live yesterday, are currently hard at work on an update to address these issues. The research has also been shared via the original source blog post and Black Hat USA 2024 and DEF CON 32 presentations from earlier this week.
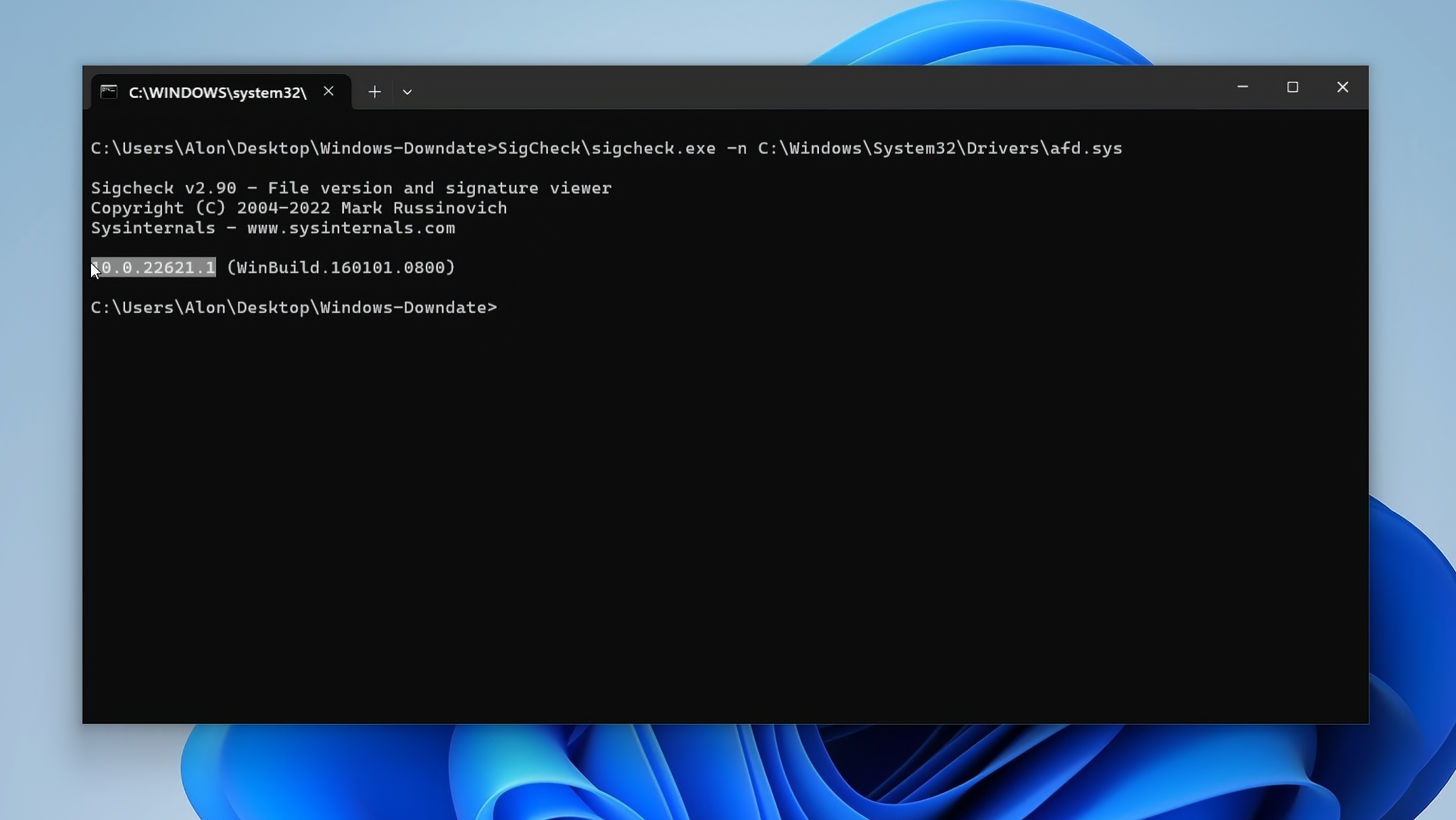
So, how does this exploit work? By utilizing a "significant flaw" in Windows Update, Windows Downdate can implement downgraded updates while bypassing all verification steps, which include integrity verification and Trusted Installer enforcement. From there, drivers, DLL files, and even the NT kernel were all made vulnerable to silent downgrades, with Windows Update and full-blown recovery/scanning tools unable to detect any problems.
Leviev's research also revealed that "the entire virtualization stack was at risk as well," which meant Secure Kernel, Hyper-V's hypervisor, and Credential Guards Isolated User Mode Process could all be exposed to past vulnerabilities. It opened up multiple ways to turn off virtualization-based security, even when enforced with UEFI locks, which generally require bypassing physical access.
The result is that any current fully patched Windows 11 machine is now susceptible to "thousands of past vulnerabilities," which effectively makes "fully patched" a meaningless term until these are genuinely fixed, per Leviev. Leviev has also observed that other OSes (older Windows, Mac, Linux, etc) may be equally susceptible to attacks like these. OS vendors need to be more vigilant regarding these attacks and existing OS features' potential as attack vectors.
Fortunately, this attack wasn't released to the wild, and it seems Microsoft should have time to fix the vulnerabilities used before exploitation becomes commonplace. However, it is still deeply concerning, considering that the VBS exploit has existed for almost a decade.








