Installing this month's Windows Server security update has knocked some enterprise domain controllers into continuous reboot cycles, Microsoft confirmed in a release health dashboard entry.
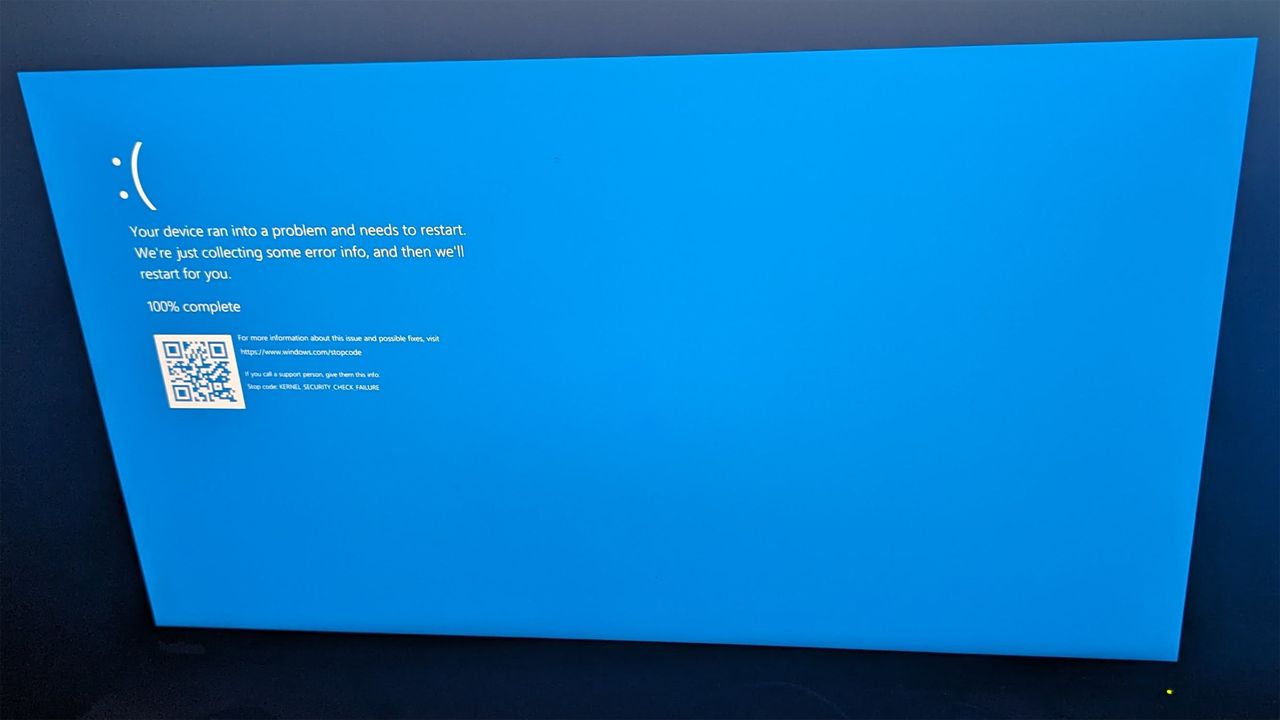
The company says the April 2026 patch, KB5082063, triggers crashes in the Local Security Authority Subsystem Service (LSASS) on non-Global Catalog domain controllers used in Privileged Access Management (PAM) deployments, leaving Active Directory authentication and directory services unavailable on affected servers.
Microsoft's dashboard lists Windows Server 2016, 2019, 2022, 23H2, and 2025 as vulnerable to the fault, with the LSASS crash occurring during the startup sequence, which is what turns the failure into a loop: each automatic reboot re-enters the same faulty authentication codepath rather than recovering into a stable state.
The problem is only affecting managed enterprise environments that run PAM for Active Directory privilege delegation, and Microsoft said personal devices outside IT-managed domains aren’t exposed. The company hasn’t yet published a patch and has instead directed affected administrators to Microsoft Support for Business for mitigation guidance that can be applied if KB5082063 is already deployed.
KB5082063 now has three acknowledged bugs within a week of release, and Microsoft has warned separately that the same update prompts some Windows Server 2025 machines for a BitLocker recovery key after installation. The company is investigating reports that KB5082063 fails to install entirely on a subset of Windows Server 2025 systems.
April security updates have disrupted Windows Server domain controllers for three consecutive years. In March 2024, Microsoft shipped an emergency out-of-band fix after that month's Patch Tuesday caused DC crashes outright. The April 2024 patch cycle then broke NTLM auth across Windows Servers and forced unplanned DC restarts, which Microsoft corrected in a May 2024 rollout.
In June last year, the company released another correction for Active Directory authentication problems introduced by the April 2025 security update. This month's LSASS crash follows the same MO for the third year running: a general Patch release followed by post-deployment failure reports from enterprise admins, and a scramble for mitigation while the fix is prepared.
With KB5082063 still on the release channel and no patch date published, admins have three choices: delay the April update, isolate a test DC to validate patch behavior before wider rollout, or escalate through the Microsoft Support form Business to obtain the mitigation steps the company is providing case-by-case.








