
Hackers are once again using fake Google Chrome updates as means to infect unsuspecting users with malware.
This time around though, they’re first going after websites and injecting scripts into them that display fake Chrome automatic update errors according to BleepingComputer.
The campaign itself began back in November of last year but in a new report, NTT security analyst Rintaro Koike explains that the hackers responsible expanded its scope in February 2023 to target even more users.
During its investigation into the matter, BleepingComputer discovered numerous sites that have been hacked in this malware distribution campaign which include news sites, online stores, blogs and adult sites as well.
Tricking visitors with fake Chrome updates

Once a website has been compromised by injecting malicious JavaScript code into it, the now hacked site executes scripts capable of downloading additional scripts when a user visits the site.
The hackers behind this campaign are using the Pinana IPFS (InterPlanetary File System) service to deliver these additional scripts as it hides the origin of the server hosting the files which makes blocking them difficult.
If a targeted user does visit one of these hacked sites, the scripts display a fake Google Chrome error screen that says they need to install an automatic update to continue to the site. From here, the scripts automatically download a ZIP file named “release.zip” which is disguised as a Chrome update.
Unsuspecting users that fall for this trick end up installing a Monero miner on their PC instead of a legitimate Chrome update. The danger with having a crypto miner like this one installed on your computer is that your system will run slower since it’s actually doing quite a lot of work in the background. At the same time though, it could also put additional stress on your CPU, GPU and other components which would then need to be replaced sooner rather than later.
Another interesting thing about this malware campaign is that the crypto miner it installs establishes persistence on a victim’s PC by adding scheduled tasks and performing Registry modifications. It also excludes itself from Windows Defender and as a result, Microsoft’s antivirus software won’t know to remove it from your system.
To make matters worse, the malware even stops Windows Update which could make your PC vulnerable to other malware strains and viruses.
How to stay safe from malware spread through fake updates
Fake updates are one the easiest ways hackers trick victims into infecting their own devices with malware. As such, you should never install any update that appears in a pop-up and this is especially true with Google Chrome.
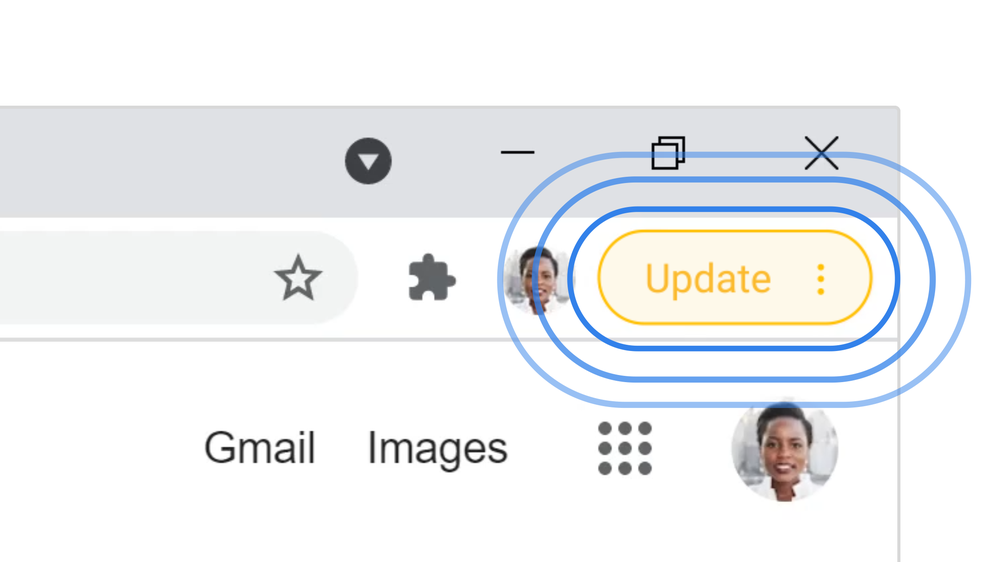
Instead of pestering you with pop-ups when a new Chrome update is available, Google instead displays a bubble next to your profile picture in the top right corner of its browser. The color of the bubble indicates when the latest update was released with green for a 2-day old update, orange for a 4-day old update and red when an update was released at least a week ago.
Clicking on this bubble will update your browser to the latest version but you can also do so manually by clicking on the three dot menu to the right of your profile picture. From here, you need to go down to the bottom of this menu and click on Help then About Google Chrome. This will take you to Chrome’s settings page and if an update is available, it will be downloaded automatically and applied the next time you restart your browser.
Besides keeping Chrome updated and avoiding pop-ups telling you to update your browser, you should also be using one of the best antivirus software solutions on your PC to help fend off malware infections and other cyberattacks.
Although this campaign is primarily targeting Japanese, Korean and Spanish speakers at the moment, NTT warns that the hackers behind it could be looking to expand further since they recently added new languages. Regardless, if you avoid pop-ups or error messages telling you to update Google Chrome, you should be safe.








