The idiom "getting more than you bargained for" is usually applied in the context of unwanted, nasty consequences. Occasionally, it's used in the literal sense, like when AI engineer Aimilios Hatzistamou found his newly-bought sleep mask unwittingly granted him access to other users' EEG data and controls.
The story is fairly simple and serves as yet another illustration of why software is almost always an afterthought for many a product. Hatzistamou bought the sleep mask as a completed Kickstarter product from "a small Chinese research company." He refrained from naming the company, but our best guess is that it could be the SLEEPU DreamPilot.
Hatzistamou's mask had recalcitrant connection issues, so he did what engineers do: took matters into his own hands. With the help of Claude Opus 4.6, he took apart the mask's Bluetooth protocol, only to find that it didn't follow any standard convention. Undeterred, he turned his attention to the Android application, which he used Claude to decompile and analyze (transcript here).
Much to no software engineer's surprise, he found some hard-coded access credentials in the app binary, apparently shared across all copies of the app (doh!), as well as the expected API endpoints for sending/receiving data remotely. Eventually, he and Claude mapped out the mask's 15 commands and functions, and had the communication protocol reasonably reverse-engineered.
It was then time to make a small web app to control the mask. That worked fine, and Hatzistamou could get his mask's information and control its functions without using the buggy Android application. Alas, that was not the end of the story. During the reverse-engineering, he had Claude poke at the remote data endpoints. When connecting to the MQTT services with the aforementioned hardcoded credentials, he did indeed get his sensor readings... along with everyone else's.
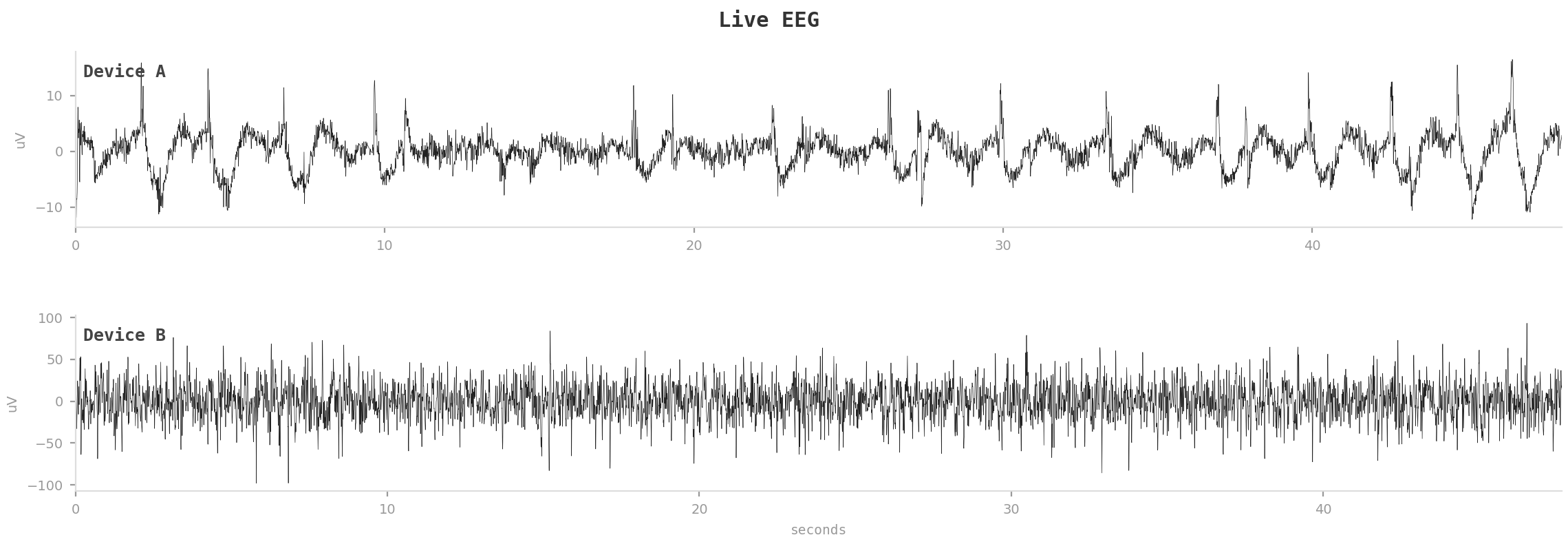
Hatzistamou estimated that among the received data, about 25 masks were in use right there and then, and he even captured the real-time EEG readings from two hapless people somewhere on the planet. Since the mask has electrical muscle stimulation (EMS) and the access credentials are the same for every device, he could theoretically tell other masks to trigger electrical impulses.
The engineer sent his findings to the company, as he actually sounds happy with the product, data issues notwithstanding. As a developer myself, this situation doesn't appear to show any malicious intent from the makers and serves as yet another unsurprising illustration of how low the bar has become for software development in this day and age.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.








