There's a new phishing security vulnerability going around, and despite it being tied to a fake Google Account security page, it's affecting a wide range of web browsers and devices, including Microsoft Edge, PCs, and phones.
Discovered by Malwarebytes (via PCGamer), the bad actors are using a convincing Google Account security page that looks like a standard security check to deploy what is being referred to as "one of the most fully featured browser-based surveillance toolkits [Malwarebytes] have observed in the wild."
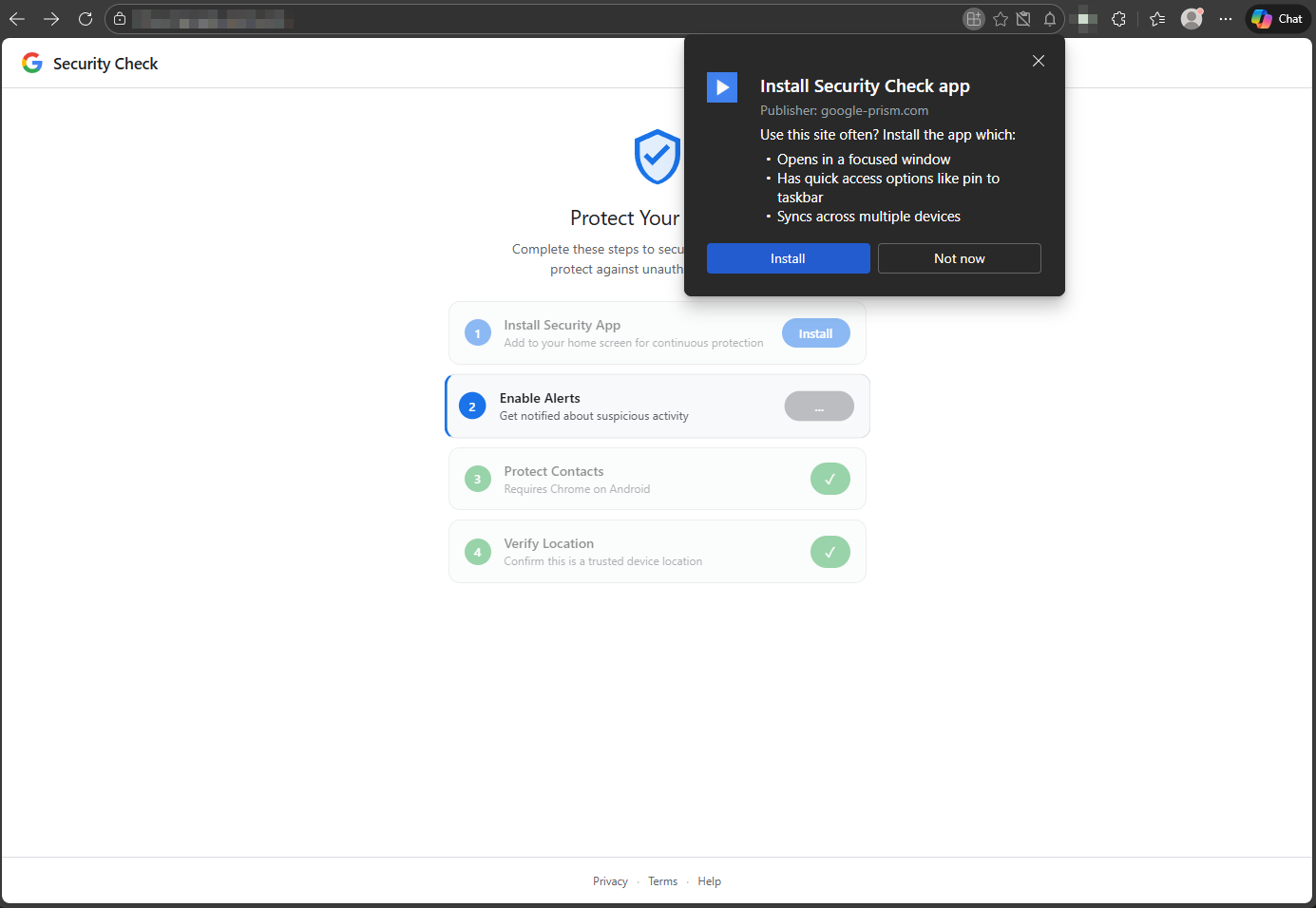
The attack does not rely on any sort of bug or exploit, which makes it particularly easy to get out into the wild. As Malwarebytes explains, each attack begins with a browser pop-up that asks you to install a Security Check app published by "google-prism.com." Of course, that is not a legitimate Google URL.
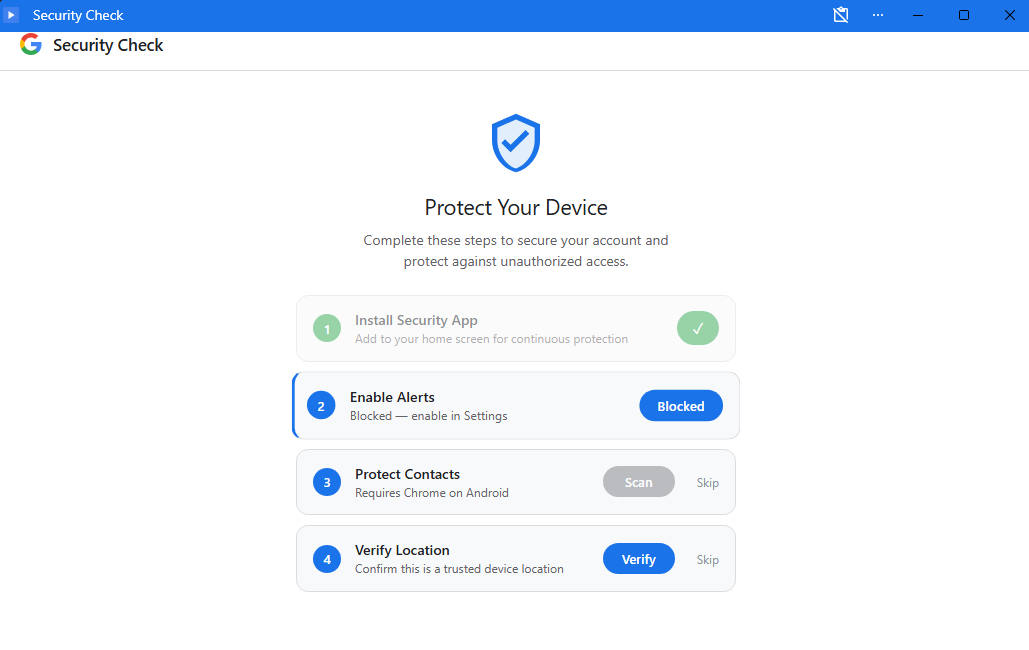
If a user opts to install the fake app, it arrives as a Progressive Web App (PWA) that looks surprisingly similar to a native Google app. It will then request specific push notification permissions disguised as the enabling of security alerts, which allows the bad actors to retain open communication even after the PWA is closed.
A legitimate Contact Picker API is fed into the PWA, and the user is asked to select contacts with whom they'd like to share the security update. The contact info is then sent back to the attacker's domain.
The last step, and perhaps the scariest, is a request for GPS location. Malwarebytes says that info, including "latitude, longitude, altitude, heading, and speed," is all sent back to the attacker's domain.
Closing the malicious PWA doesn't put an end to the vulnerability
Assuming a user falls for the trick and installs the PWA, closing it doesn't put an end to the vulnerability.
When the app is open, it can read clipboards to try and find passwords and wallet addresses, intercepting SMS codes used for verification at the same time. When the app is closed, this portion isn't active. However, a "service worker" remains active. Here's how Malwarebytes explains it:
It sits underneath the page, handling push notifications, running background tasks embedded in push payloads, and queuing stolen data locally when the device goes offline, then flushing that queue the moment connectivity returns. It includes handlers for background and periodic sync events, allowing it to wake and execute tasks where those features are supported and registered.
Malwarebytes
So, while you can stop the clipboard and SMS data harvesting by closing the PWA, the service worker continues operating. With the right notification permissions, it's capable of waking, pushing new tasks, and triggering data uploads.
Bad actors can use your browser as if it's their own
The vulnerability goes from bad to worse, as Malwarebytes explains how bad actors can make it look like their web traffic is coming from your browser on your IP.
This is achieved via a connection to a WebSocket relay with the installed malware acting as a proxy. Not only is this a terrifying prospect in terms of blackmail or conspiracy, but it can also compromise corporate networks.
How to check if your Windows PC has been compromised
Malwarebytes lays out the steps required to check if your Android, macOS, iOS, and Windows devices have been compromised, with steps to help you remove the malicious PWA.
I recommend you run through the steps as soon as possible, even if you don't remember installing anything related to a Google Security Alert. It's better to be safe than sorry.
What do you think about this browser vulnerability affecting Edge users?
Were you affected by this new form of malware discovered by Malwarebytes? Are you concerned about how malware is evolving to not require any bug or exploit? Let me know in the comments section!

Join us on Reddit at r/WindowsCentral to share your insights and discuss our latest news, reviews, and more.








