Update, 3:15pm PT: AMD shared a comment on the new vulnerability disclosure, which we've added below.
Original Article, 9:16am PT : A new paper released by security researchers at the Technical University of Berlin reveals that AMD's firmware-based Trusted Platform Module (fTPM / TPM) can be fully compromised via a voltage fault injection attack, thus allowing full access to the cryptographic data held inside the fTPM in an attack called 'faulTPM.' Ultimately this allows an attacker to fully compromise any application or encryption, like BitLocker, that relies solely upon TPM-based security.
The researchers accomplished this feat using off-the-shelf componentry that cost roughly $200 to attack AMD's Platform Security Processor (PSP) present in Zen 2 and Zen 3 chips. The report does not specify if Zen 4 CPUs are vulnerable, and the attack does require physical access to the machine for 'several hours.' The researchers have also shared the code used for the attack on GitHub and a list of the inexpensive hardware used for the attack.
The report is especially pertinent now that Microsoft has added TPMs to its system requirements for Windows 11, a move met with resistance due to its deleterious impact on gaming performance even when it works correctly, and severe stuttering issues when it does not. Yes, the TPM requirement is easily circumvented. Still, Microsoft's push for the feature has increased the number of applications relying solely on TPM 2.0 for security features, thus increasing the cross-section of applications vulnerable to the new faulTPM hack.
We reached out to AMD for comment, and the company issued the following statement to Tom's Hardware:
“AMD is aware of the research report attacking our firmware trusted platform module which appears to leverage related vulnerabilities previously discussed at ACM CCS 2021. This includes attacks carried out through physical means, typically outside the scope of processor architecture security mitigations. We are continually innovating new hardware-based protections in future products to limit the efficacy of these techniques. Specific to this paper, we are working to understand potential new threats and will update our customers and end-users as needed.” — AMD spokesperson to Tom's Hardware.
To our understanding, the papers released at ACM CCS 2021 centered around a glitching attack, but did not use the attack vector to compromise the TPM. Instead, the attack was used to defeat Secure Encrypted Virtualization. As such, this new research reveals a novel method whereby AMD's fTPM can be fully compromised.
As a reminder, discrete TPMs plug into a motherboard and communicate with the processor to provide security, but the external bus between the CPU and TPM has proven to be hackable with multiple different approaches. As such, the firmware TPM, or fTPM, was created to embed the functionality inside of the chip, thus providing TPM 2.0-class security without an easily-hackable interface exposed to attackers.
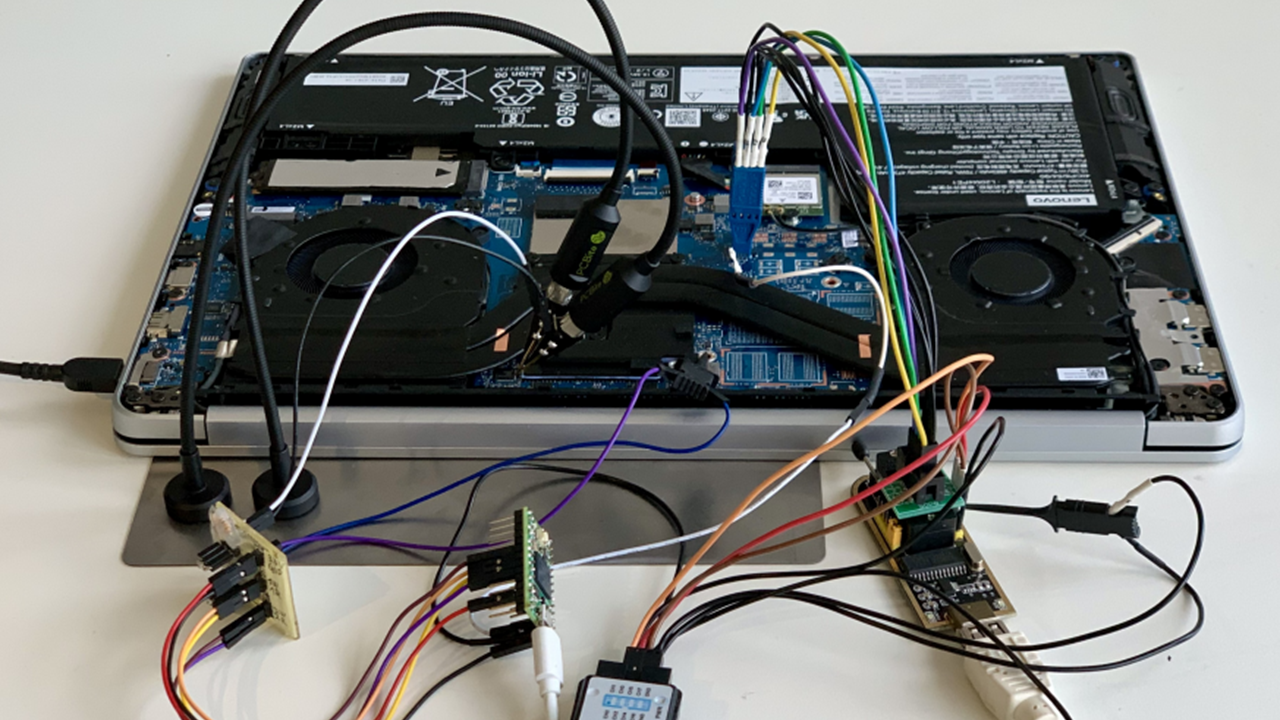
The faulTPM attack centers on attacking the fTPM, which, to our knowledge, hasn't been possible before. As you can see from the above picture of the Lenovo Ideapad 5 Pro system the researchers used to execute the attack, this isn't a simple endeavor and will require a few hours of physical access to the machine. In the case of nation-states or the highest-end levels of espionage or corporate espionage, this is fairly easy to accomplish, though.
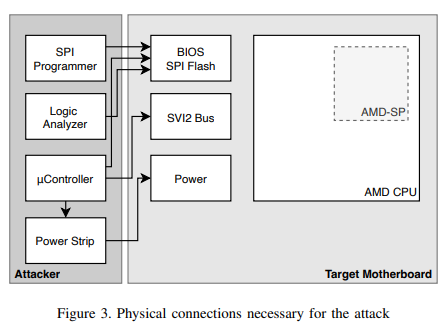
Here we can see the multiple connections to the power supply, BIOS SPI chip, and SVI2 bus (a power management interface) the researchers used on the Lenovo test subject. These connections are used to execute a voltage fault injection attack against the PSP present in Zen 2 and Zen 3 CPUs, thus acquiring the chip-unique secret that allows the decryption of the objects stored within the TPM. Here's the step-by-step method of attack:
- Backup the BIOS flash image using an SPI flash programmer
- Connect the fault injection hardware and determine the attack parameters (4.1)
- Compile & deploy the payload extracting the key derivation secret (4.3)
- Start the logic analyzer to capture the extracted key derivation secrets via SPI
- Start the attack cycle on the target machine until the payload was executed successfully
- Parse & decrypt the NVRAM using the BIOS ROM backup and payload output with amd-nv-tool
- Extract and decrypt TPM objects protected by this fTPM with amd ftpm unseal
The researchers successfully gained full access to the TPM and the data sealed within, thus allowing them to compromise the BitLocker Full Disk Encryption (FDE) on the device. As one would imagine, this would lead to full access and control of the device, and all of the data contained therein, in relatively short order.
By default, BitLocker uses a TPM-only mechanism to store the keys, but users can manually enable a PIN setting that allows the user to assign a PIN code that works in tandem with the TPM-based mechanisms. However, these PIN codes aren't enabled by default and are vulnerable to brute-force attack methods. Simple numerical PINs are relatively easy to break, but more rigorous text-based passphrases are harder to crack.
As mentioned, this attack also exposes applications that only use TPM-based security, while applications with multiple layers of security will be more secure.
The researchers contend that this attack vector isn't easy to mitigate due to the voltage fault injection, so the earliest intercept point for AMD to fix the issue would presumably be with its next-gen CPU microarchitectures. According to the researchers, Intel's Converged Security and Manageability Engine (CSME) prevents these types of attacks.
We haven't seen any official communication from AMD on the matter, so the release doesn't appear to be part of an industry-standard coordinated disclosure. We've contacted AMD for more details on the attack and to see if the company has a mitigation plan. We'll update as necessary.








